Free Certificate Of Destruction Template. If company coverage requires that completely different network entry policy be applied based on consumer security group membership, computer-only authentication is generally not an option. Or, should you solely want a single certificates template, head over to GraphicRiver and download your editable certificates template design. Your color scheme ought to mirror the sort of certificate you’re giving out in addition to your workplace.
Click on each textual content box and sort in information to personalize your certificates. Your certificates could not print accurately out of your browser window. To add special symbols to your text, click on on the text block and then click on the A button on the left facet of the subheader to see all textual content modifying options. Find the Special Symbols button and choose those you need from a drop-down list.
But before we dive into the free templates, let’s take a glance at a few premium certificate templates. While premium templates are an funding in your business, in addition they provide you with more customization options as nicely as a extra polished look. Using these printable certificate Free Certificate Of Destruction Template on your events, you will find create a professional one has by no means been easier. When we saw the optimistic impression this program was having on folks all over the world, we wished to increase into further fast-growing, high-paying career fields – Project Management, Data Analytics and UX Design. These certificates, built and taught by Google, are designed to arrange individuals from all backgrounds for jobs where there’s great demand for certified candidates.
Click right here to see a few of the many shoppers that use SecureW2 to harden their community safety. Find out why so many organizations rely upon SecureW2 for his or her network security. Using the shapes or by importing design elements from your individual gadget, develop a theme.
Objects tab in the menu on the left accommodates varied components for making your designs more particular person. To add a new object to your design, please choose an appropriate factor on the left and click on it or drag it on the canvas. Use the Delete button in the editor or the Backspace button in your keyboard or just drag the item beyond the artboard to remove it.
We will problem a statutory certificates against EU SRR or Statement of Compliance (for non-EU flagged ships including the UK). We can even problem a Statement of Compliance against HKC on the identical time for no further cost. Our simple, tried and examined IHM Free Certificate Of Destruction Template is carefully designed towards legislative requirements and permits simple compilation and upkeep of the IHM.
For this example, the chosen certificates shall be Workstation Authentication. In Windows Server 2012, the potential of renewing a certificate with the identical key was introduced. This functionality will work when shoppers that beforehand received a Free Certificate Of Destruction Template which may be configured for renewal with the same key try to renew it. Windows Server 2012 and Windows eight can implement certificates renewal with the identical key. 11.Close your browser when you’ve finished in order that no extraneous certificates could be created should you walk away from the enrollment station without logging off.
Make Amazing Free Certificate Of Destruction Template
You can use this certificate PDF Free Certificate Of Destruction Template to present students with a beautifully designed certificate, something they’ll cherish for years to come back. Next we’ll configure our machine authentication; our EAP Method might be EAP-FAST and we’ll want to leave all of the defaults that present up after that. Make a observe of the option to use unauthenticated PAC provisioning; ensure that is off except there’s a actually good purpose you need it. Instead, authenticated PAC provisioning will verify the certificates offered by ISE before the change, making certain that the shopper trusted the endpoint.
One flat charge will get you limitless downloads from a huge assortment of professional content. This spectacular certificate template obtain is available for each Microsoft Word and Adobe Photoshop. Use it as a free editable certificate of appreciation template or a certificate of completion Free Certificate Of Destruction Template free for use. Motivate your employee or students by recognizing a job well done. Create a great wanting certificates rapidly and easily utilizing an editable certificate template. If you might be looking for a way to enthusiastically rejoice and express your appreciation for someone’s achievement, check out the Microsoft certificate templates collection.
When scheduling the examination, be sure to choose the 2-week timeframe recommended, so you get the maximum number of slots obtainable. The Front-end Developer Specialization examination focuses on the fundamentals of OutSystems Front-end improvement. Targeted for Front-end developers which are pretty autonomous in creating UI designs and stylings to achieve pixel-perfect internet and cellular purposes. Gain the information and abilities to streamline your product improvement course of, create high-performing product designs and manufacturing system layouts, and connect your group and knowledge from design by way of manufacture. If you use an permitted food premises you are nonetheless required to apply for a Temporary Food Service for off-site food sales.
Pictures of Awesome Free Certificate Of Destruction Template

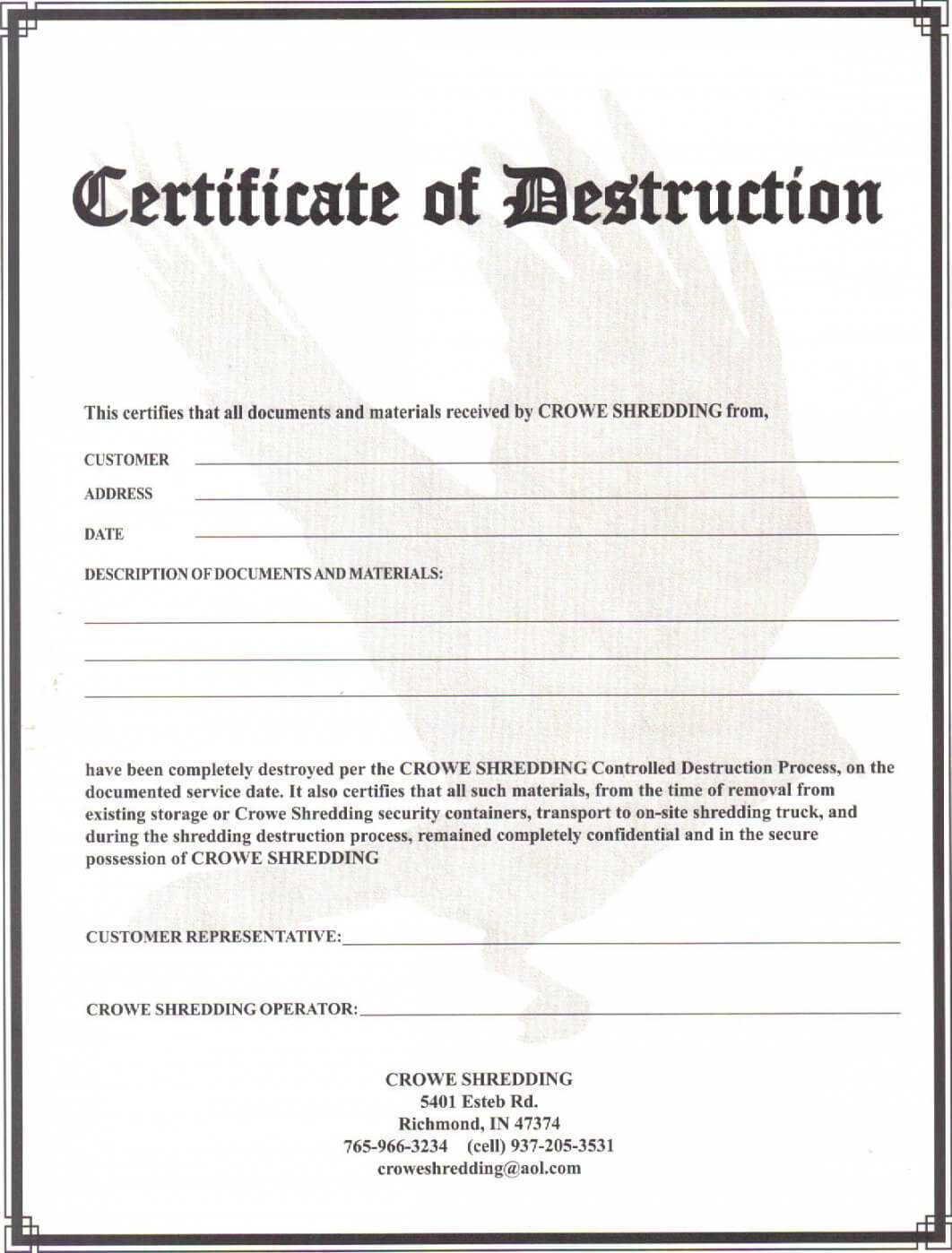
038 Certificate Of Destruction Template Ico Exceptional within Free Certificate Of Destruction Template
004 Certificate Of Destruction Template Free Form intended for Free Certificate Of Destruction Template
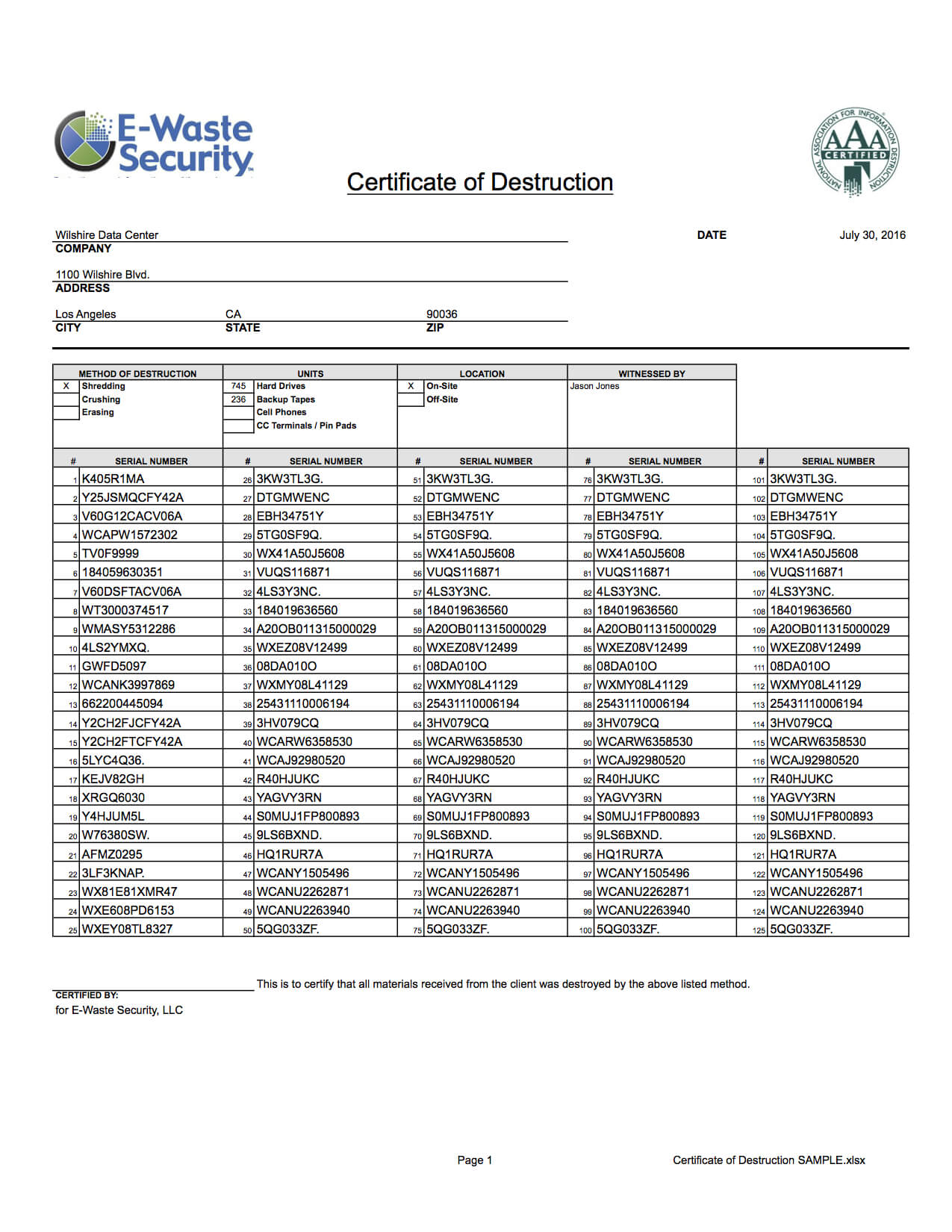
Certificate Of Destruction – Hard Drive Destruction – E within Free Certificate Of Destruction Template

016 Certificate Of Destruction Template Ideas Bunch For in Free Certificate Of Destruction Template

🥰5+ Free Certificate Of Destruction Sample Templates🥰 for Free Certificate Of Destruction Template

Free Printable Certificate Of Destruction Sample inside Free Certificate Of Destruction Template
045 Sample Certificate Data Destruction And Greenchip Of pertaining to Free Certificate Of Destruction Template
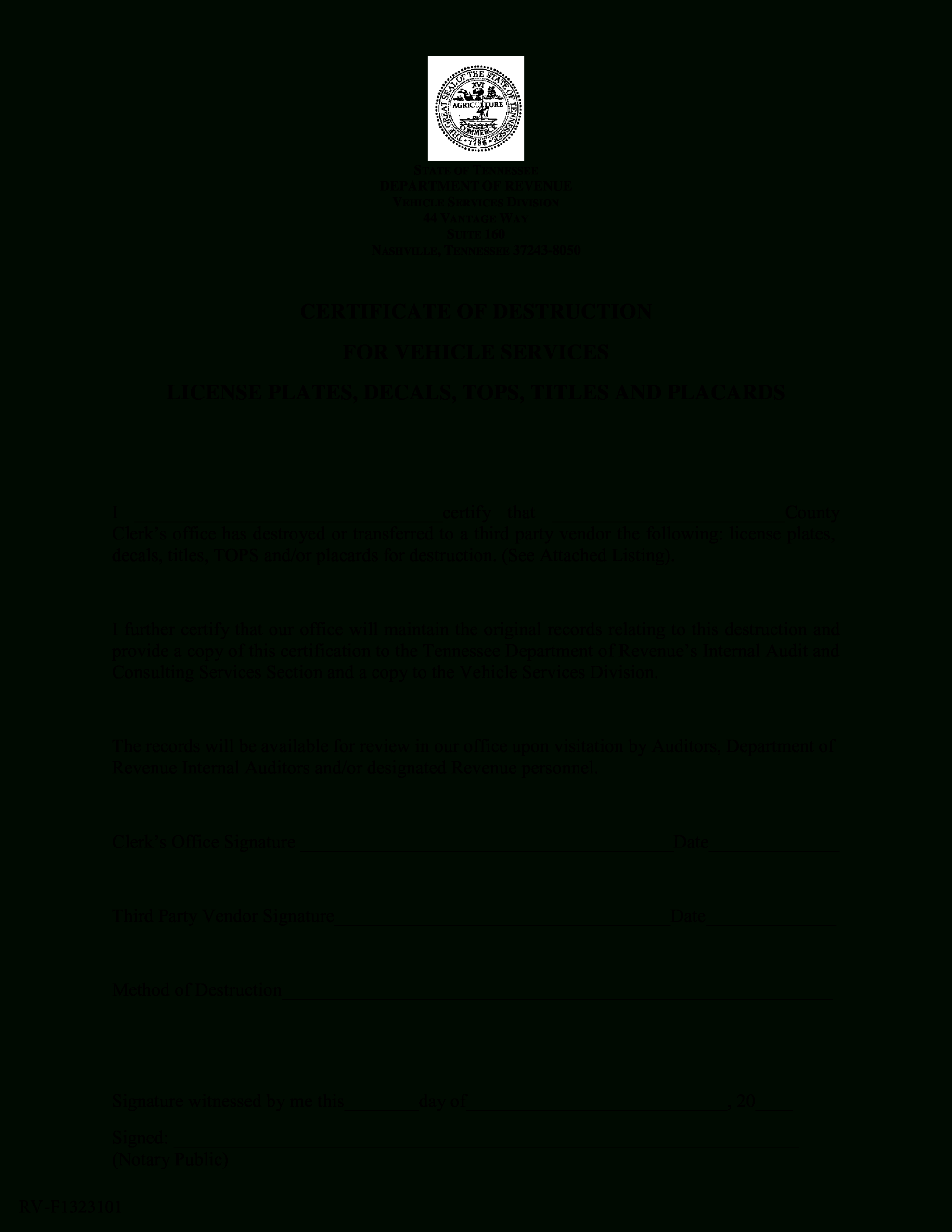
Vehicle Certificate Of Destruction | Templates At throughout Free Certificate Of Destruction Template
Simple Certificate Of Destruction | Templates At in Free Certificate Of Destruction Template

Hard Drive Destruction Certificate Template intended for Free Certificate Of Destruction Template
Blank Certificate Of Destruction | Templates At intended for Free Certificate Of Destruction Template